Check Point Research (CPR), the Threat Intelligence arm of Check Point® Software Technologies Ltd., a leading provider of cybersecurity solutions globally, has published its new Brand Phishing Report for Q1 2021. The report highlights the brands which were most frequently imitated by criminals in their attempts to steal individuals’ personal information or payment credentials during January, February and March.
In Q1, Microsoft was again the brand most frequently targeted by cybercriminals, as it was in Q4 2020. Thirty-nine percent of all brand phishing attempts were related to the technology giant (down slightly from 43% in Q4), as threat actors continued to try to capitalise on people working remotely during the Covid-19 pandemic. DHL maintained its position as the second most impersonated brand, with 18% of all phishing attempts related to it, as criminals persisted in taking advantage of the growing reliance on online shopping.
The report reveals that technology is still the most likely industry to be targeted by brand phishing, followed by shipping. However, banking has replaced retail in the top three industries this quarter, as two banking brands – Wells Fargo and Chase – are now in the top ten list, showing how threat actors are exploiting the surge in digital payments due to the pandemic, and the increased dependency on online banking, shopping and home deliveries, to try and trick users and commit financial fraud.
“Criminals increased their attempts in Q1 2021 to steal peoples’ personal data by impersonating leading brands, and our data clearly shows how they change their phishing tactics to increase their chances of success,” said Omer Dembinsky, Data Research Manager at Check Point. “While security measures are often built into websites and apps, particularly with banking, it’s the human element that often fails to pick up on scams, and as such, cyber criminals are continuing to trick people using convincing emails purporting to be from trusted brands. As always, we encourage users to be cautious when divulging personal data and credentials, and to think twice before opening email attachments or links, especially emails that claim to be from companies, such as banking institutions, Microsoft or DHL, that are the most likely to be impersonated.”
In a brand phishing attack, criminals try to imitate the official website of a well-known brand by using a similar domain name or URL and web page design to the genuine site. The link to the fake website can be sent to target individuals by email or text message, a user can be redirected during web browsing, or it may be triggered from a fraudulent mobile application. The fake website often contains a form intended to steal users’ credentials, payment details or other personal information.
Top phishing brands in Q1 2021
Below are the top brands ranked by their overall appearance in brand phishing attempts:
- Microsoft (related to 39% of all brand phishing attempts globally)
- DHL (18%)
- Google (9%)
- Roblox (6%)
- Amazon (5%)
- Wells Fargo (4%)
- Chase (2%)
- LinkedIn (2%)
- Apple (2%)
- Dropbox (2%)
DHL phishing email – malware example
During the first quarter of 2021, we observed a malicious phishing email that used DHL’s branding and was trying to download the Agent Tesla RAT (Remote Access Trojan) to the user’s machine. The email (see Figure 1) which was sent from a webmail address and spoofed to appear as if it was sent from support@dhl.com, contained the subject, “DHL Import Clearance – Consignment : <number>”. The content asked to download an archive file “DHL-IVN.87463.rar”, which contains a malicious executable file that would cause the system to be infected with Agent Tesla.

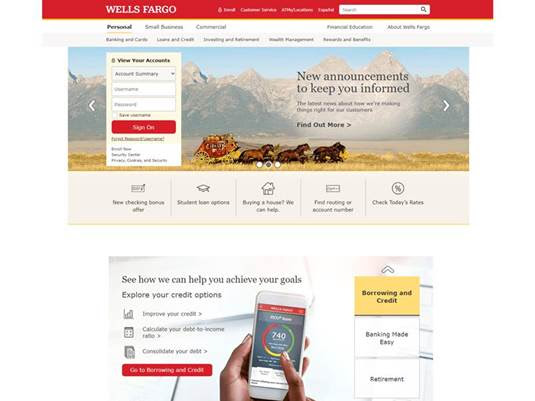
Wells Fargo phishing email – account theft example
In this phishing email, we see an attempt to steal a user’s Wells Fargo account information. The email (see Figure 2) which was sent from the spoofed email address noreply@cc.wellsfargo.com, contained the subject, “Your Online access has been disabled”. The attacker was trying to lure the victim to click on a malicious link, which redirects the user to a fraudulent malicious page that looks like the real Wells Fargo website (see Figure 3). In the malicious link, the user was prompted to key in their username and their password.

Check Point’s Brand Phishing Report is powered by Check Point’s ThreatCloud intelligence, the largest collaborative network to fight cybercrime, which delivers threat data, and attack trends from a global network of threat sensors. The ThreatCloud database inspects over 3 billion websites and 600 million files daily, and identifies more than 250 million malware activities every day.




Share your thoughts